Research data: Top vulnerabilities in the IoT systems
When you budget for IoT security testing, am I investing the money effectively?
Simply based on the industry news, a massive portion goes into device testing, analyzing the firmware of a device and protocol fuzzing. We tend to visualize IoT hacking as an adversary penetrating an IoT system from the device.
But our deep-dive analysis of the Common Vulnerabilities and Exposures (CVE) landscape reveals a different reality. By analyzing data from the National Vulnerability Database (NVD), CISA’s Known Exploited Vulnerabilities, and IoT malware reports, we found that focusing solely on the "thing" in the Internet of Things is a strategic error.
1. The 10% Reality: It’s Not About the Device
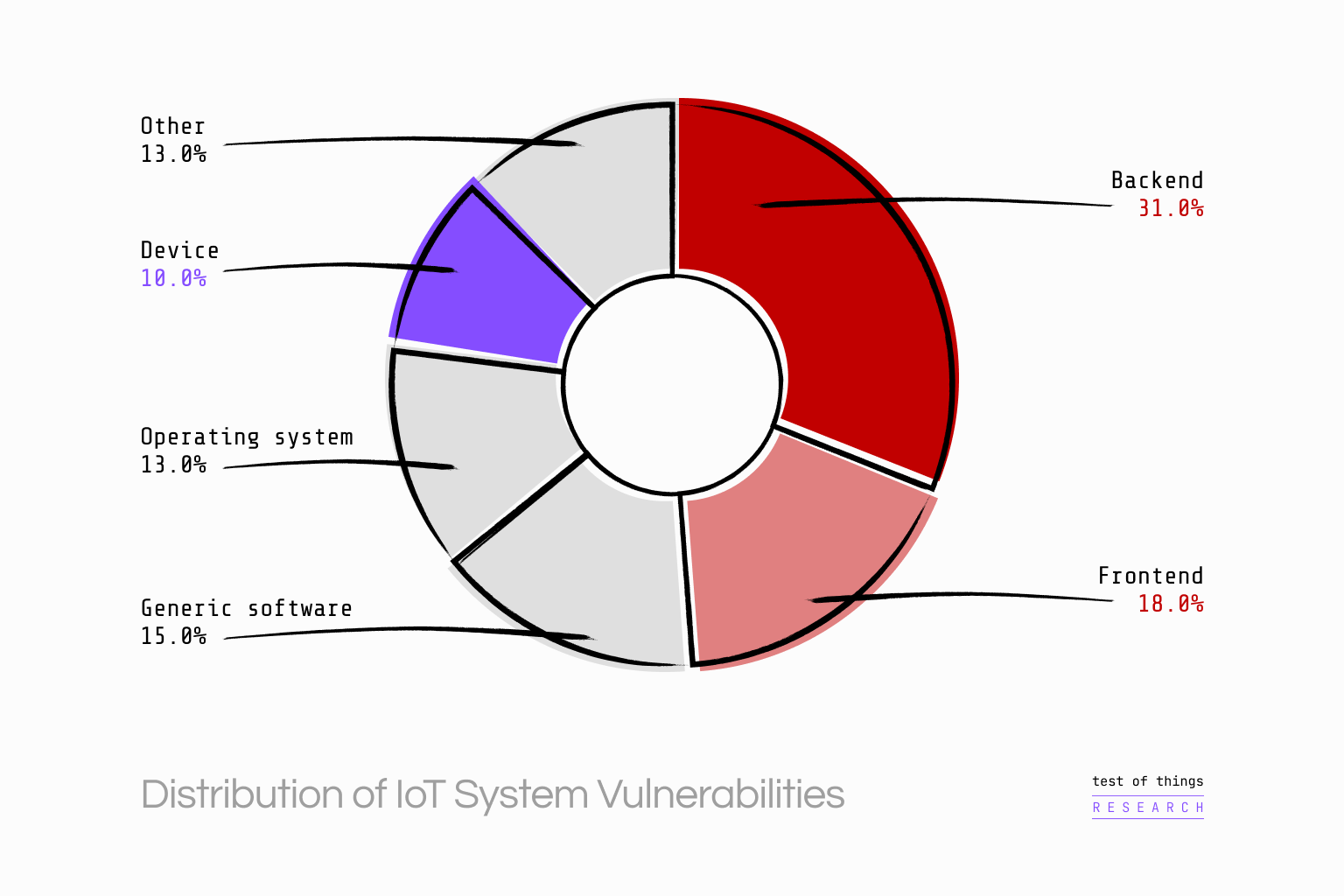
The most interesting finding from our analysis of CVE data is how few vulnerabilities are actually located in the IoT device hardware or firmware logic itself.
Only 10% to 14% of analyzed vulnerabilities were specific to the IoT device.
Where are the rest?
31% reside in the Backend (cloud/server).
18% reside in the Frontend (web interfaces/APIs).
13% reside in the OS.
15% reside in generic Software Components.
If your testing strategy is device-centric, you are ignoring nearly 90% of the attack surface. The "boring" IT stack—the cloud APIs and web frontends—is where the real volume of risk lies.
Half of all IoT vulnerabilities exist in the cloud and user interfaces, not the device itself.
2. HTTP: The Unexpected "Root" of All Evil
While we worry about exotic protocols like Zigbee or proprietary Bluetooth implementations, attackers are exploiting the protocol we use every day: HTTP.
Our analysis of IoT malware revealed a staggering statistic: 92% of vulnerabilities used in IoT malware targeted HTTP servers.
Why? Because HTTP servers are complex, ubiquitous, and difficult to secure. They are the "vulnerability hotspots" of the IoT ecosystem. Whether it is the local web server on a router (Network Device) or the REST API endpoint in the cloud (Backend), HTTP is the primary attack vector.
This simplifies the testing roadmap. Before you invest in custom fuzzers for proprietary protocols, ensure your HTTP implementation is bulletproof.
3. The "Injection" Epidemic
What specific weaknesses are attackers exploiting via these HTTP vectors? It isn't always complex memory corruption.
In our analysis of vulnerabilities exploited by IoT malware, 82% were Injection vulnerabilities (CWE-74).
This confirms that IoT security is not fundamentally different from web security. The same SQL injection and command injection flaws that have plagued the web for two decades are now fueling botnets like Mozi. Attackers prefer these vulnerabilities because they are easy to exploit and offer high impact—often leading to remote code execution.
4. The Mobile App Blind Spot
The mobile application is often the forgotten component of the IoT ecosystem. It is treated as a UI, not a security boundary.
However, our research highlights a different story. Mobile app vulnerabilities are dominated by Improper Authentication (CWE-287) and Exposure of Sensitive Information (CWE-200).
Furthermore, studies show that IoT-related mobile apps frequently request far more permissions than necessary, violating the principle of least privilege. If your mobile app can read location data or access storage without cause, it becomes a high-value target for compromising the user's privacy, regardless of how secure the device firmware is.
The Strategic Takeaway: Holistic Defense
The data is clear: An IoT system is not just a device; it is a distributed system comprising devices, mobile apps, frontends, and backends.
If you are in an executive management responsible for product compliance, your compliance strategy must reflect this:
Shift Left on Web Security: Treat your IoT backend and device web servers with the same rigor as your corporate web applications (OWASP Top 10).
Audit the Chain: Do not just test the firmware. Test the mobile app permissions, the API authentication, and the cloud infrastructure.
Manage Components: With 15% of vulnerabilities found in software components, a robust Software Bill of Materials (SBOM) strategy is not optional—it is essential for vulnerability management.
At Test of Things, we don't just test the "thing." We test the entire system. Our tool-driven assessments cover the device, the cloud, and the connections between them, ensuring you aren't left vulnerable by the 90% of risks that standard device testing misses.