Research: Navigating the Overlaps and Gaps in 16 IoT cybersecurity requirements
Product security teams are staring down a fragmented regulatory landscape. The EU Cyber Resilience Act (CRA), the US Cyber Trust Mark (NIST), ETSI EN 303 645, FDA guidance, and IEC 62443 all demand your attention.
A common, dangerous assumption in IoT product development is that building to one rigorous standard will inherently satisfy the others. However, our deep-dive research into global IoT security requirements proves this false.
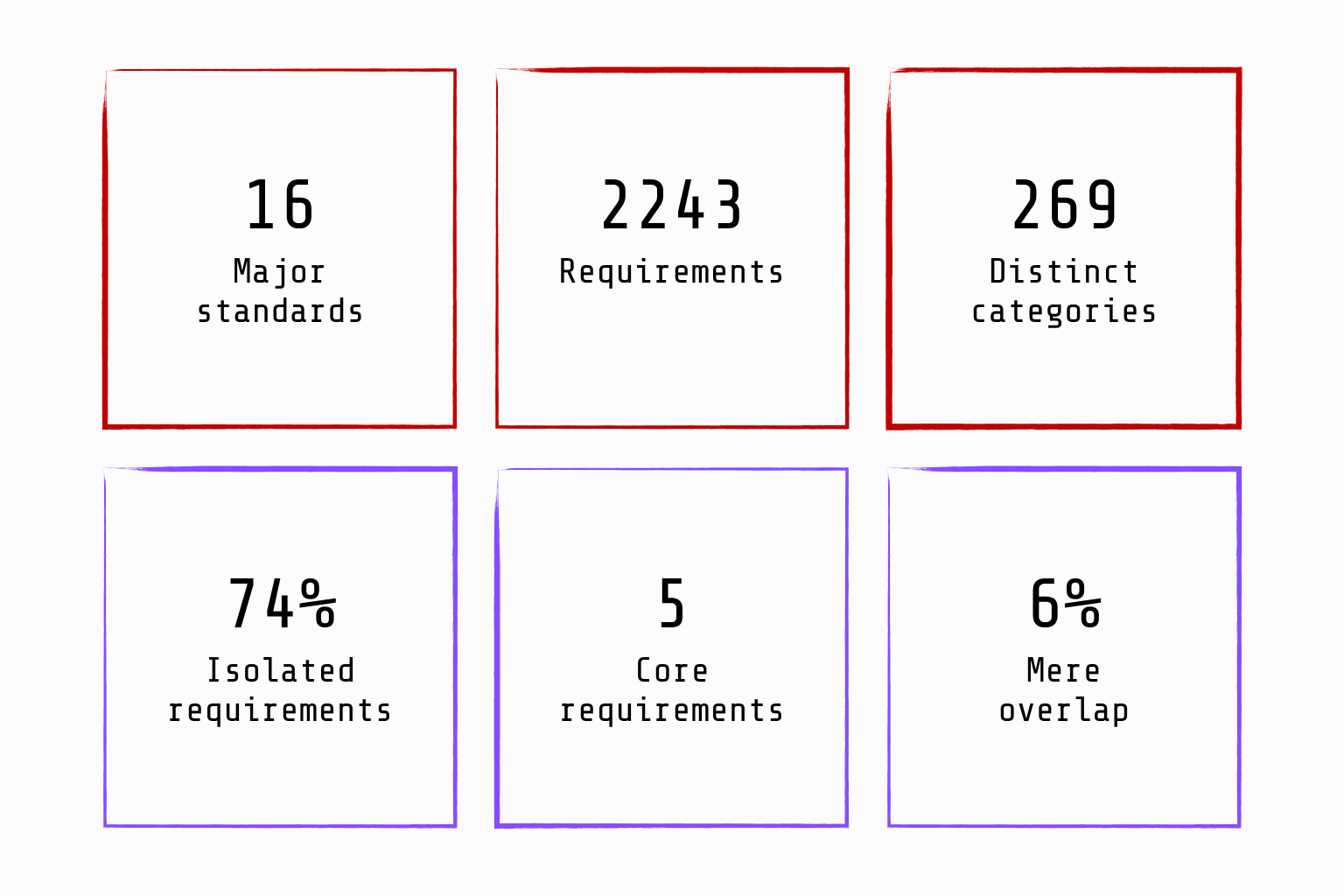
At Test of Things, we systematically analysed 2,243 individual security requirements across 16 major sources*—including ETSI, NIST, FDA, GSMA, and ioXt—to understand exactly where global standards overlap and where they uniquely diverge.
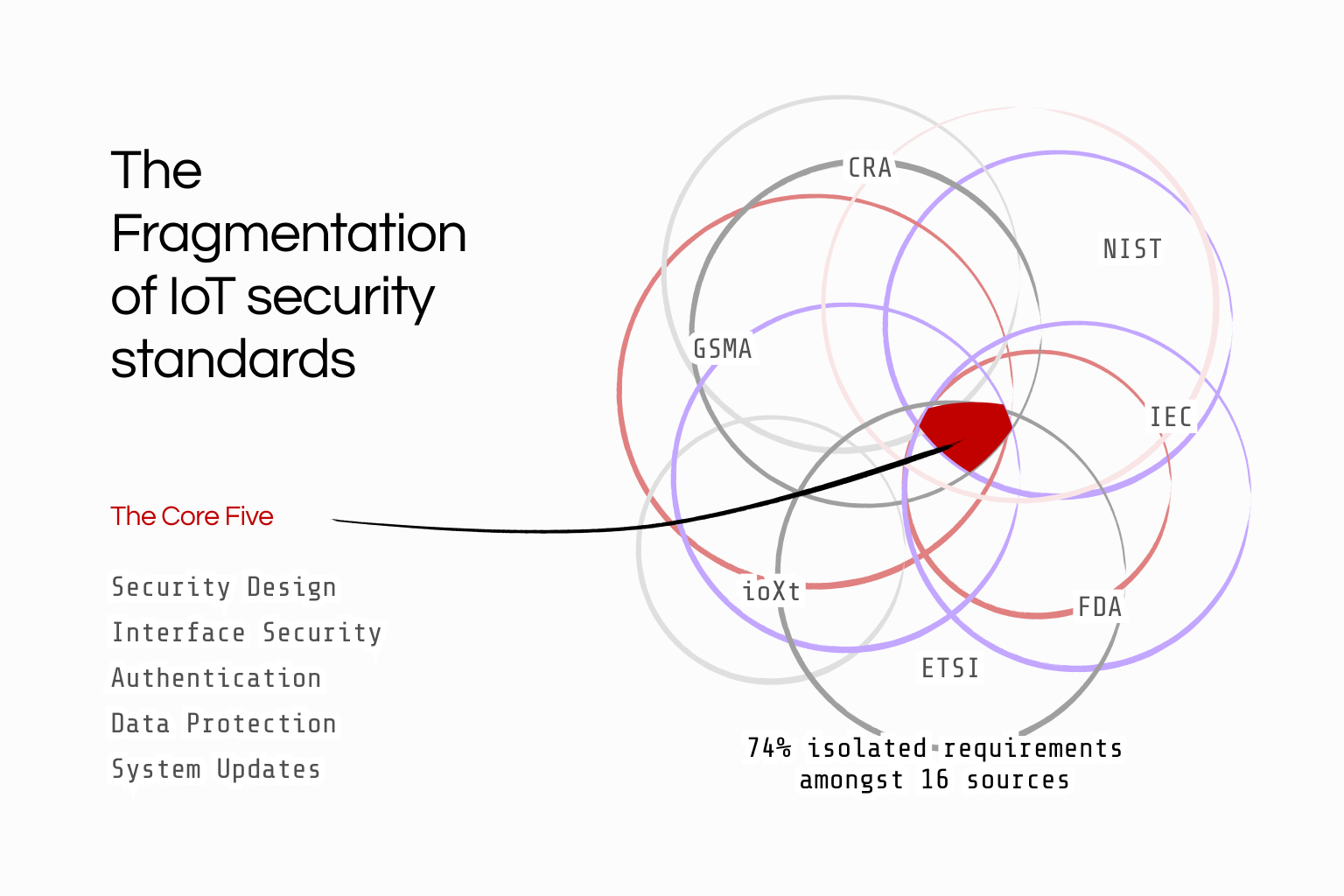
The Overlap: The "Core Five" requirement categories
To make the 2,243 diverse requirements comparable, we consolidated them into 269 distinct categories.
When we looked for universal consensus, the results were interesting. Out of the 16 major standards, guidelines and best practices analysed in the research, all of them shared only five product requirement categories:
Security Design: Defining the security architecture, subsystems, and enforcing the principle of least privilege.
Interface Security: Minimising attack surfaces, closing unused interfaces, and rigorously validating external inputs.
Authentication: Protecting against brute force attacks and securing component/user identity.
Data Protection: Encrypting data in transit and at rest.
System Updates: The capability to securely update the system over time.
Alongside these product features, 14 out of the 16 sources agreed on three life-cycle (process) requirements: deriving security requirements from risk analysis, adhering to recognised security standards over proprietary methods, and executing continuous vulnerability management.
These foundational elements are your non-negotiables. Because they are universally demanded, verifying them should be the baseline for any cybersecurity assessment practice. Automating the verification as far as possible would be even better.
The Baseline Consensus
The Divergence: The 74% Fragmentation Trap
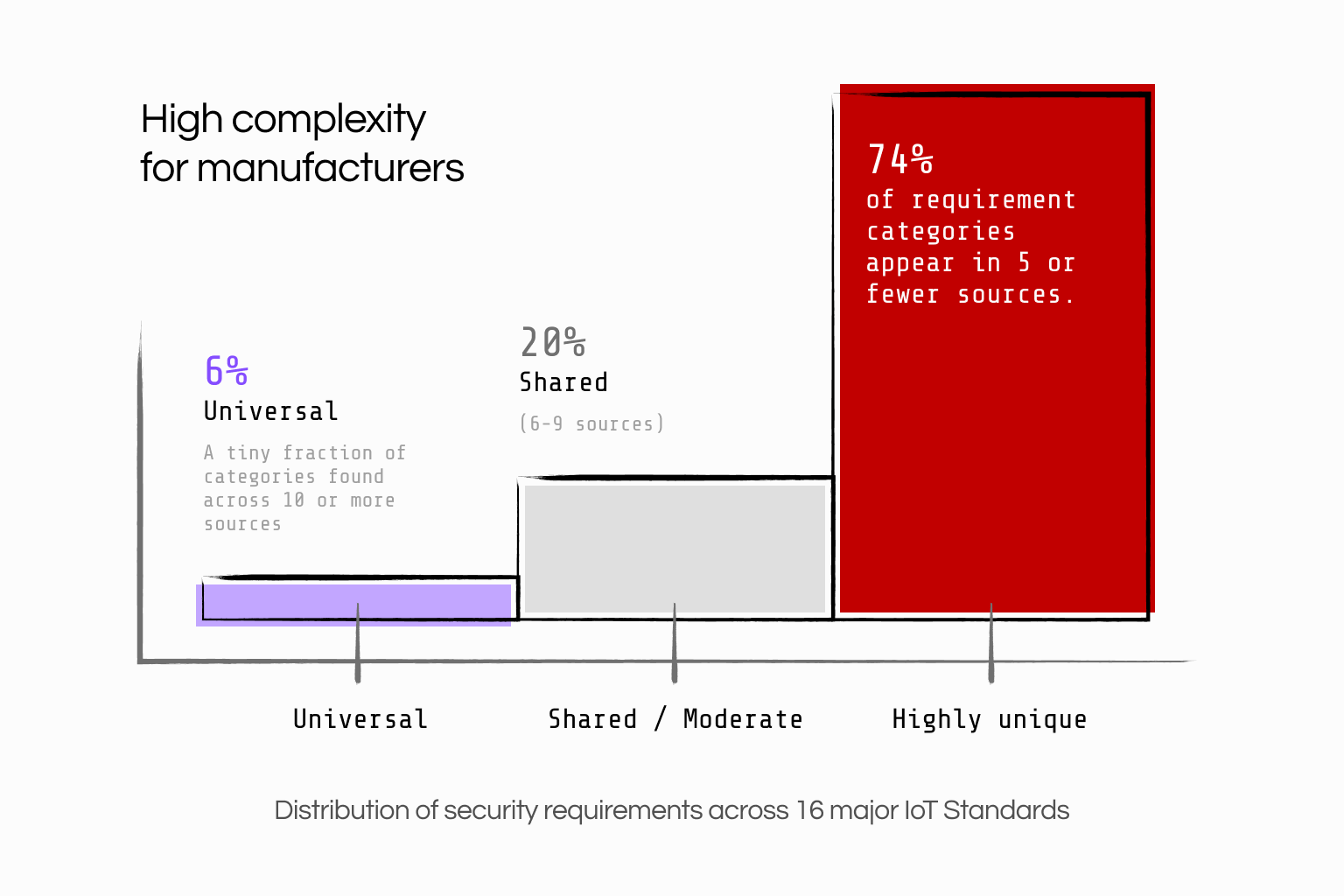
While the "Core Five" provide a baseline, they represent a fraction of the overall regulatory picture.
Our research revealed a great degree of fragmentation also: Only 6% of requirement categories appear in 10 or more sources.
The "long tail" of unique requirements is massive. We found that 74% of security requirement categories are present in five or fewer sources. On average, any given standard has 5% entirely unique categories and shares 38% of its requirements with only 2 to 5 other sources.
Consider these unique divergences:
While every standard demands Data Protection, highly specific privacy requirements (like strictly defining collected private data and establishing data decommissioning protocols) are surprisingly rare in technical standards.
A manufacturer attempting to leverage an ETSI EN 303 645 certification for a medical device (FDA) or an industrial control system (IEC 62443) will find that the detailed sub-requirements for tamper protection, physical inspection, or secure hardware fundamentally differ.
Two different security standards will likely have significant variation in their requirements. Conforming to a new standard doesn't just mean ticking a few extra boxes; it introduces entirely new paradigms of unique requirements that increase the workload.
The Fragmentation of IoT cybersecurity standards requirements
The Strategic Imperative: Stop Manual Mapping
The days of relying on spreadsheet-based manual mapping to navigate compliance are over. The sheer volume of unique, non-overlapping requirements makes it a mathematically losing battle.
To achieve sustainable IoT cybersecurity, your strategy must evolve:
Automate the Consensus: Utilise tool-driven security assessments to automatically verify the 6% of requirements that every standard agrees on. Tools like Nmap, ZAP, and Testssl.sh can verify your attack surface, web interfaces, and TLS encryption continuously without manual intervention.
Declare Your Security Posture: Move away from opaque "penetrate-and-patch" testing. Instead, use a machine-readable threat model to define your specific architecture, components, and the unique security controls you've implemented. This model then can be automatically tested to be accurate continuously.
Focus Experts on the Divergence: By automating the baseline, your Cyber Security Engineers and Consultants can dedicate their time to the complex, unique requirements demanded by specific sector regulations—such as proprietary authentication protocols or hardware tamper resistance.
At Test of Things, we don't just provide you with another checklist. Our tool-driven security assessment methodology maps exactly to the complex DNA of global standards, automating the overlaps and illuminating the gaps. If your business requires adhering to multiple local and global cybersecurity requirements, we can help you with automated assessments as well as automated compliance work.
*List of IoT cybersecurity standards, guidelines and best practices used on the research:
C2 IoT Security Baseline
CTIA C.security Test Plan
Cybersecurity Label
ENISA Security Baseline
ETSI EN 303 645
FDA Draft Guidance
GSMA IoT Sec. Assessment
ISASecure CSA
IMDA IoT C.security Guide
Internet Society IoT Trust
IoT Security Initiative
IoTSF Security Compliance
IoT Acceleration Consortium
NCSC Health Requirements
NHTSA Best Practises
NISTIR 8259a